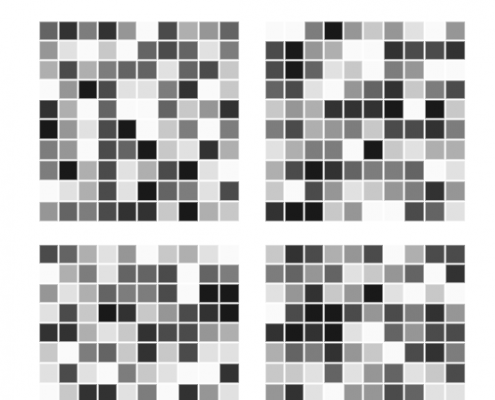
Order is something humans have an absolute obsession with, we spend our lives classifying, organising and labelling the world around us. We are so good at it that we have invented computers to help us order things faster and more efficiently. Solving a puzzle is incredibly rewarding as a human, one of the reasons for this is you are collapsing something that looks random (such as the letters in a word search) and revealing the order in the chaos. So, for a species so obsessed with order, is it possible to be random? Can we create truly random sequences of numbers and avoid creating subconscious patterns?
To test this out we have created three games below, click on each one and find out how random you can be:
As you may have discovered, humans are not very random at all, which also goes for computers. Computers are at a fundamental level calculators, performing simple arithmetic such as adding. Like baking a cake a human has to give them a set of instructions and ingredients which they then follow to the letter to produce a result. Whereas this is excellent for doing maths, their simple determinism makes them poor at producing anything “randomly”.
How do computers create random numbers?
Computer-based random number generators are mathematical functions that output a random-looking sequence of numbers when fed a number known as “seed”. The same seed will always give the same sequence of numbers. Furthermore, given enough time, these sequences eventually will repeat themselves. A good example of this occurring is an exploit in the game Pokemon emerald, where players can guarantee the type of Pokemon they obtain by waiting a fixed amount of time.
To avoid this issue the “seed” needs to be updated at regular intervals and be random. Classically, seeds are chosen using signals which are complex and hard to predict, such as the number of clicks a person performs with a mouse. This kind of random number generation is often called pseudo-random, as despite appearing random their generation at a fundamental level is deterministic.
The problem with pseudo-random
In some applications, the distinction between a pseudo and a true random number is irrelevant. Take for example video games; RNGs are used to generate content, or determine the outcome of battles in a single player game. This is sufficiently random for this application, therefore it is not necessary to use a true random number generator.
However, when pseudo-random number generators are used for cryptography they can be exploited to obtain personal information, or intercept personal communications. This is a very real problem; in November 2017 a group of scientists from several universities showed that the widely used crypto-system RSA, could be attacked by exploiting its poor random number generation.
Currently, the best solutions are based on hard to predict random events. Hardware random-number generators (HRNGs) produce numbers which are much more difficult to predict than pseudo-random numbers, because they are based on physical processes.These could include thermal noise, radioactive decay, or shot noise through an electronic circuit. Cloudflare, an online security company, has a wall of lava lamps, which record how the wax inside moves. This produces a hard to predict sequence of random numbers.
These HRNG solutions generate relatively unpredictable random numbers, but they can be influenced. For instance, if the temperature of the lava lamps on the wall was altered, it would effect the numbers being produced. For this reason, a RNG that cannot be predicted or influenced is needed (see our solution).